
API Compliance: Why Regulators Care About Your APIs
Why API observability and compliance are now a regulatory priority?
APIs have become the primary channel through which sensitive financial, healthcare, and personal data moves across enterprises, and regulators have caught up. Frameworks like PCI DSS 4.0, GDPR, DORA, and PSD2 now explicitly require API-level visibility, traceability, and security controls.
Why is this shift happening now?
● 99% of organizations experienced at least one API security incident in the past year, making APIs the most targeted attack surface in regulated industries
● PCI DSS 4.0 became fully enforceable on March 31, 2025, with mandatory API audit trails and 12-month log retention requirements
● DORA went into effect on January 17, 2025, requiring EU financial institutions to demonstrate continuous API monitoring and operational resilience
● GDPR penalties reaching 4% of global annual revenue now apply to API-level data flow violations
● Shadow APIs, undocumented endpoints invisible to compliance tools, exist in over 20% of enterprise API inventories and represent immediate regulatory exposure
For regulated enterprises, API observability is no longer optional infrastructure. It is the mechanism through which compliance is proven, audited, and maintained.
Below, we explore which frameworks explicitly require API observability, what makes shadow APIs a compliance liability, and how enterprises can build compliance-ready API infrastructure.
What do regulators say about API observability and compliance?
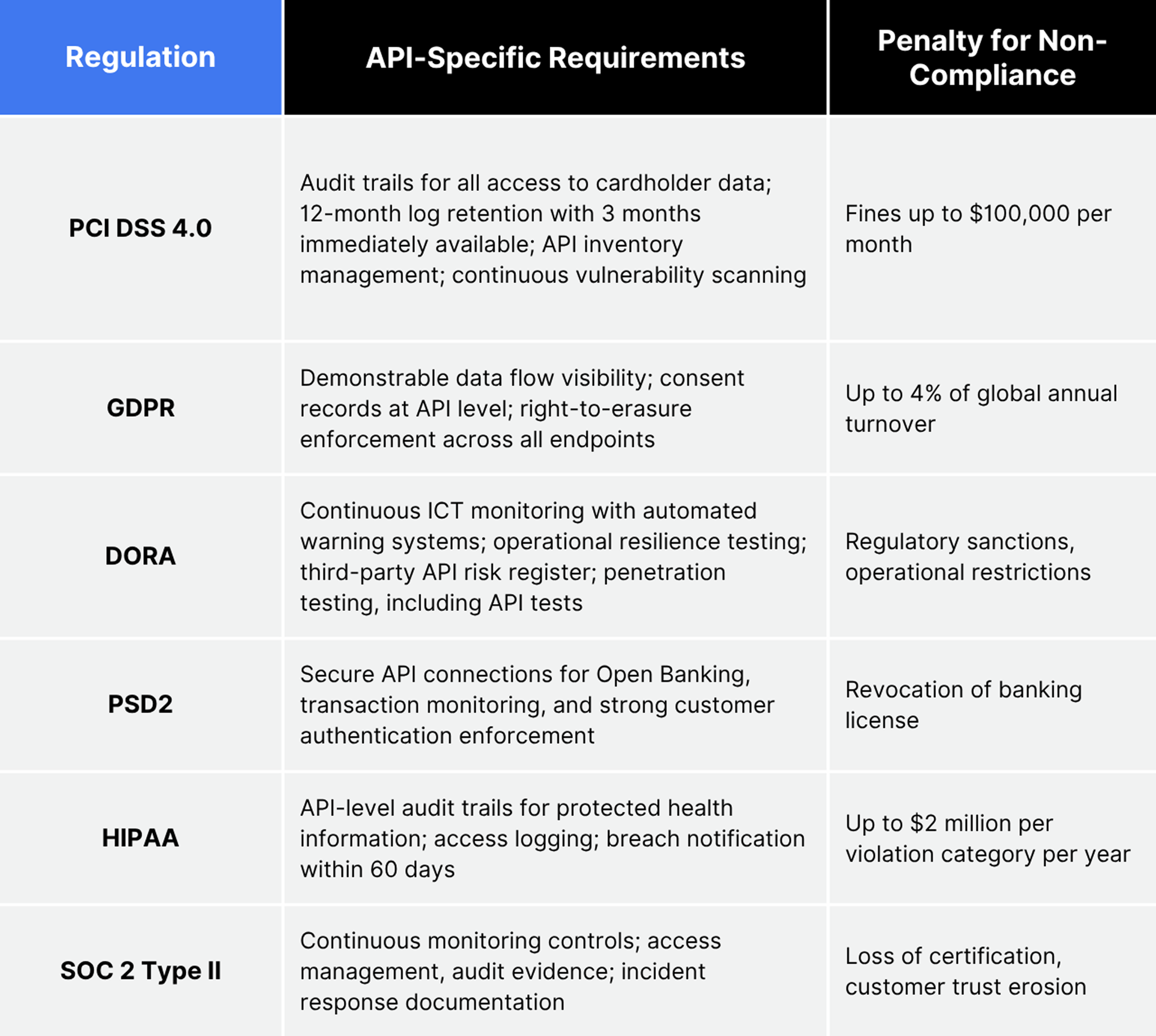
Each major compliance and regulatory body has moved from treating APIs as an implementation detail to explicitly mandating API-level controls.
PCI DSS 4.0, fully enforced as of March 31, 2024, now requires organizations to maintain full audit trails that capture user identification, event type, timestamps, and affected data, with logs retained for a minimum of 12 months, with 3 months immediately available for analysis. The standard explicitly addresses API security controls and web application protections as mandatory, no longer best-practice recommendations.
DORA (Digital Operational Resilience Act), effective January 17, 2025, mandates that EU financial institutions demonstrate operational resilience across all information and communication technology (ICT) services, including real-time performance monitoring, automated warning systems, prevention of unauthorized access, data loss, and third-party risk management.
GDPR requires demonstrable visibility into what personal data flows through which APIs and who accesses it. PSD2 Open Banking regulations require secure, auditable API connections between banks and third-party providers.
Why are regulatory bodies from across the globe bringing APIs into their regulatory purview at the same time?
API attack traffic has grown by approximately 600% in recent years, and compliance frameworks, including NIST SP 800-53, SOC 2, and ISO 27001, have begun explicitly addressing API security in their requirements.
What regulations require API observability?
Multiple regulatory frameworks now require the kind of visibility that only API observability provides: real-time monitoring, audit trails, access logs, and anomaly detection across all API traffic.
The common thread across every framework: the ability to see, trace, and prove what your APIs are doing.
That capability is observability.
Why are shadow APIs a compliance liability?
Shadow APIs are undocumented endpoints created outside official governance processes, are the single largest compliance blind spot in most enterprises. You cannot comply with regulations about data flows you cannot see.
Shadow APIs account for over 20% of the total API inventory in the average enterprise. Only 21% of organizations report a strong ability to detect API attacks, and shadow APIs are invisible to detection tools that don't know they exist. The OWASP API Security Top 10 (2023) lists Broken Object Level Authorization (BOLA) as the #1 vulnerability. Shadow APIs are especially susceptible because they bypass standard authorization controls entirely.
High-profile breaches at T-Mobile (37M records) and Optus (10M accounts) both originated from API endpoints that existed outside any governance process. The misconfigurations were basic, but no compliance control covered endpoints that were never cataloged.
Why compliance teams should care:
● An undiscovered API handling PCI-scoped cardholder data creates an immediate PCI DSS violation.
● A shadow API processing EU personal data without consent records violates GDPR from the moment it goes live.
● DORA requires financial institutions to maintain a complete register of all ICT arrangements. Shadow APIs are by definition missing from that register.
● HIPAA demands access logging for all protected health information. Unmonitored APIs create gaps auditors will find.
How does API observability enable compliance?
API observability enables compliance by providing the three capabilities regulators demand but that traditional monitoring cannot deliver: complete API discovery, real-time audit trails, and continuous generation of compliance evidence.
The difference between monitoring and observability matters here. API monitoring tells you an API is up. Observability tells you which APIs handle regulated data, who accessed them, when, and whether access controls were enforced. Monitoring generates alerts. Observability generates audit evidence.

What this looks like in practice:
● Automated API discovery across every endpoint, including shadow APIs that auditors will eventually ask about
● Real-time audit trails satisfying PCI DSS 4.0's 12-month log retention and 3-month immediate availability requirements
● Data flow mapping showing exactly which APIs handle regulated data (PII, PHI, cardholder data) and who accesses it
● Continuous monitoring providing the operational resilience evidence DORA requires
What is the cost of API non-compliance?
The cost of API non-compliance extends far beyond fines. It includes operational restrictions, reputational damage, customer attrition, and, in the most severe cases, loss of operating licenses.
Apart from the penalties, there are numerous other hidden costs that come with non-compliance. This include:
● Mandatory forensic audits costing $500K to $2M+ per incident
● Customer notification requirements triggering churn
● Increased insurance premiums and audit frequency
● Board and executive liability exposure
Imperva and Thales estimate that API-related security incidents lead to up to $186 billion in annual enterprise losses. A single undetected shadow API handling regulated data can trigger penalties that exceed the cost of an observability platform by orders of magnitude.

How do you build a compliance-ready API infrastructure?
Building compliance-ready API infrastructure requires four capabilities applied across every API gateway in your environment: complete API discovery, unified audit logging, automated policy enforcement, and continuous compliance monitoring.
Step 1: Discover every API
Deploy automated API discovery across all environments. Catalog every endpoint, including shadow APIs, zombie APIs, and third-party integrations. Classify each API by data sensitivity level: PCI-scoped, PII-handling, PHI-handling, public, or internal.
Step 2: Implement unified audit logging
Centralize API transaction logs across all gateways into a single audit trail. Capture user identity, endpoint, timestamp, request/response metadata, and outcome for every call. Enforce a 12-month audit log retention policy for compliance purposes.
Step 3: Automate governance policies
Embed compliance checks across your API environment. Enforce authentication standards (OAuth 2.0, mTLS) automatically before deployment. Block APIs that fail security scanning from reaching production. Automated linting against OpenAPI specifications catches policy violations at build time, not audit time.
Step 4: Monitor continuously
Real-time anomaly detection across all API traffic. Automated alerting for compliance deviations: authentication failures, unauthorized data access, and rate limit violations.
What are common API compliance mistakes?
The most common API compliance mistakes are treating security and compliance as separate problems, relying on gateway-level monitoring alone, and assuming documented APIs are the only APIs that matter.
Mistakes to avoid:
● Conflating security with compliance. A secured API is not necessarily a compliant API. Compliance requires provable audit trails, data flow documentation, and evidence of continuous monitoring, not just encryption and authentication.
● Gateway-only visibility. 31% of organizations run multiple API gateways (Postman 2025). Each gateway has its own dashboard and its own blind spots. Compliance requires a unified view across every data plane.
● Manual API inventories. Manual documentation is always incomplete and always outdated. Automated discovery is the only way to maintain an accurate, auditable API inventory that satisfies DORA's register requirements.
● Periodic compliance audits. Conduct periodic internal audits to ensure every endpoint is accounted for, every detail is logged, and every component of your API infrastructure is compliant.
● Ignoring third-party APIs. Regulatory frameworks hold you responsible for the data handled by third-party APIs you consume. DORA explicitly requires third-party ICT risk management with a complete contractual register.
How does APIwiz help enterprises achieve API compliance?
APIwiz provides the observability and governance infrastructure that regulated enterprises need to prove compliance, not just claim it. Because it sits above any API gateway or service mesh as a federated control plane, it delivers unified visibility that fragmented, gateway-specific tools cannot provide.
Key compliance capabilities:
● Zero-touch API discovery across multi-cloud, multi-gateway environments, finding every API, including shadow and zombie endpoints regulators will ask about
● Real-time audit trails with full transaction logging across every endpoint
● Automated governance policy enforcement integrated into CI/CD pipelines
● Compliance-ready dashboards mapped to PCI DSS, GDPR, DORA, and HIPAA requirements
● Data flow mapping showing which APIs handle regulated data and who accesses it
● eBPF-powered observability providing kernel-level tracing with near-zero performance overhead
Enterprise customers in banking and financial services, including RCBC, Commercial Bank of Qatar, and digital neobank Tonik, use APIwiz to manage thousands of APIs, with full-lifecycle governance and compliance monitoring across their entire stack.
Key takeaways
API compliance is no longer a checkbox exercise for regulated enterprises. It is a continuous, observable, and provable discipline. Regulations such as PCI DSS 4.0, DORA, and GDPR now explicitly require the kind of API-level visibility that only full-stack observability can provide.
Shadow APIs, fragmented gateway monitoring, and manual inventories are compliance liabilities hiding in plain sight. The enterprises that invest in automated API discovery, unified audit trails, and continuous compliance monitoring will pass their next audit and avoid the fines, restrictions, and reputational damage that come from flying blind.
Book a demo to see how APIwiz delivers compliance-ready API observability across any gateway, any cloud.
FAQs about API compliance
What is API compliance, and why does it matter?
API compliance is the practice of ensuring that all APIs meet the security, audit, and data-handling requirements of applicable regulatory frameworks, including PCI DSS 4.0, GDPR, DORA, HIPAA, and SOC 2. It matters because APIs are now the primary channel for sensitive data in regulated industries, and non-compliance can expose organizations to financial penalties of up to 4% of annual turnover under the GDPR alone.
Which regulations specifically require API observability?
PCI DSS 4.0 requires full audit trails for all access to cardholder data, with a 12-month log retention period. DORA mandates continuous ICT monitoring with automated warning systems for EU financial institutions. GDPR requires demonstrable visibility into personal data flows. HIPAA demands access logging for protected health information. All of these frameworks effectively require API-level observability to achieve full compliance.
What is a shadow API, and why is it a compliance risk?
A shadow API is an undocumented endpoint created outside an organization's official governance and security processes. Shadow APIs handle data without the audit trails, access controls, or monitoring that regulators require. If a shadow API processes cardholder data or personal data without proper controls, the organization is in violation from the moment that API goes live, often without knowing it.
How does API observability differ from API security for compliance purposes?
API security protects APIs against threats: authentication, encryption, rate limiting, and input validation. API observability provides the visibility and evidence that compliance requires: audit trails, access logs, data flow mapping, and continuous monitoring. Compliance requires both security to protect the data and observability to prove to regulators that you're protecting it.
What are the penalties for API-related compliance failures?
Penalties vary by framework: GDPR fines can reach 4% of annual global revenue, with Meta's €1.2 billion fine in 2023 the largest to date. PCI DSS fines can reach up to $100,000 per month. HIPAA violations carry penalties up to $2 million per category per year. Beyond direct fines, organizations face mandatory forensic audits, increased insurance premiums, and executive liability.
How do you prove API compliance to auditors?
Proving compliance requires continuous, exportable evidence: unified audit trails that show every API transaction with user identity and timestamp; a complete API inventory that includes shadow and third-party endpoints; automated governance policy enforcement records; real-time monitoring dashboards that show anomaly detection and incident response; and data flow maps that show which APIs handle regulated data. Manual spreadsheets and periodic snapshots no longer satisfy modern regulatory standards.
Effortless API Management at scale.
Support existing investments & retain context across runtimes.
.png)
Effortless API Management at scale.
Support existing investments & retain context across runtimes.
.png)


